In order to be more open and lessen any worries about privacy and safety, Nord Security (Nord) has made their Linux NordVPN client and its related networking libraries source code available to the public.
Yesterday, Nord declared that the MeshNet private tunneling feature, which is part of their VPN, is now attainable without cost for anybody who downloads the software, regardless of whether or not they pay for the service.
NordVPN users have the ability to create private connections to other users of the service, granting them the possibility to access the web through the shared network or internal devices like individual gaming servers.
In concurrence with its announcement, NordVPN has published the source code for its Linux applications and two libraries, Libtelio and Libdrop.
Nord has publicly declared their dedication to transparency and responsibility by releasing their products as open source, as stated in their announcement.
The coding community’s input and examination is essential to us, and we trust in the quality of our software.
Nord Security’s GitHub page now holds all three projects, featuring comprehensive instructions on building the NordVPN Linux and libraries. Link provided.
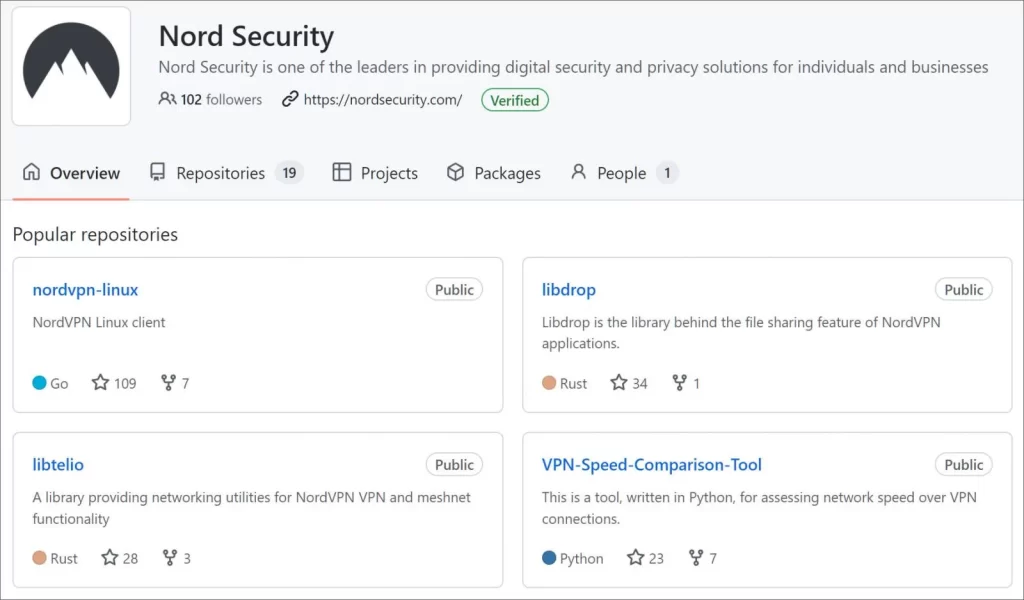
LibDrop, which is a component of Nord’s MeshNet, provides a convenient way for users to transfer files securely and privately through a tunnel.
Nord claims that the LibTelio networking library is widely used across all NordVPN applications on any platform it’s available, and it is responsible for forming encrypted networks using the MeshNet feature.
Nord explains that making Libtelio open source is particularly significant since it is used as the basis for all the NordVPN applications, not simply their Linux client.
By entrusting the Linux community with this material — one of the most colorful open-source domains currently in operation — we are hoping to motivate capable coders and developers to investigate our code and improve our service.
The source code for the NordVPN Linux application is available for download and compilation, and NordVPN encourages users to customize it as desired.
Nord Security implores users to check the source code carefully and report any bugs they might uncover.
Those who identify security weaknesses in the Linux client can share them with Nord Security’s bug bounty program, hosted on HackerOne. For critical errors, the company offers rewards of $10,000 to $50,000.